Product Security Developments
For the last few years, the Cyber Resilience Act (CRA) has been a topic of high-level policy debate. As of late 2025, that phase is over. With the adoption of new implementing regulations and significant shifts in EU agency roles, the CRA has entered its operational phase.
For manufacturers, importers, and distributors of digital products, help and guidance are available. Here is a breakdown of the four critical developments that have reshaped the CRA landscape over the last two months.
1. The Mystery is Over: Important Products Defined
The Update: The European Commission has adopted Implementing Regulation (EU) 2025/2392.
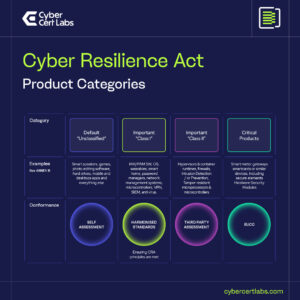
Why it Matters: Until now, the CRA divided products into Default, Important, and Critical categories, but the definitions were broad. Manufacturers of routers, smart home devices, or identity management software were often unsure where they landed. This new Regulation provides the precise technical descriptions for these categories. This is the single most important document for your legal team right now. It is the difference between performing a cheaper self-assessment (Class I) or being forced to pay for a mandatory third-party conformity assessment (Class II or Critical). If your product roadmap includes products with digital elements, you must cross-reference your features against this text immediately.
Link https://eur-lex.europa.eu/legal-content/EN/TXT/?uri=CELEX%3A32025R2392
2. The Digital Omnibus: A Promise of Simplicity
The Update: The Commission has published the Digital Omnibus Regulation Proposal.
Why it Matters: One of the industry’s biggest fears has been overlapping reporting. A single data breach could theoretically trigger reporting requirements under the GDPR (72 hours), NIS2 (24 hours), and the CRA (24 hours), involving different regulators and different forms. The Digital Omnibus is the EU’s answer to this friction. It proposes a Single Reporting Point, effectively harmonising the incident reporting flow across these directives. While this is still a proposal, it signals that the EU is listening to industry concerns regarding administrative burden. It aims to let security teams focus on patching the breach rather than filling out three different government forms.
Read more here – https://www.cybercertlabs.com/case_studies/what-will-the-digital-omnibus-proposal-means-for-incident-reporting-under-eu-regulations/
3. ENISA’s New Global Status
The Update: ENISA (The European Union Agency for Cybersecurity) has been designated as a CVE Program Root.
Why it Matters: The CRA mandates that manufacturers report actively exploited vulnerabilities to ENISA. Critics questioned whether ENISA had the capacity to handle this influx of data. By becoming a CVE Root (joining the ranks of CISA and MITRE), ENISA has secured the operational authority to issue CVE IDs and manage vulnerability disclosures autonomously. This confirms that the CRA will not just be a legal text, but a technical ecosystem. It establishes digital sovereignty for the EU, ensuring that European vulnerability data is managed within the bloc while remaining compatible with global standards.
4. The Implementation Official Guidance
The Update: The Commission’s updated CRA Implementation Fact page.
Why it Matters: With the regulation entering into force with a 36-month transition period, now only 24 months remain. The first obligations around vulnerability reporting will come into effect September 2026 with the remaining obligations becoming applicable December 2027. This fact page covers guidance for manufacturers, the role of market surveillance and Member States, the role of the open-source community for the implementation of the CRA and supports of tools available to support SMEs and start-ups. The CRA-AIproject is delighted to be part of the official guidance in the SME section!
Link to CRA Fact Page: https://digital-strategy.ec.europa.eu/en/factpages/cyber-resilience-act-implementation

Conclusion
The CRA is no longer coming; it is here. The product definitions are written, the reporting structure is being simplified, and the agency in charge (ENISA) is working up its technical capabilities. The time for debate is over; the time for preparing has begun!
If you are an SME in scope you can get a FREE CODE for a Readiness Assessment by emailing the CRA-AI project at cra-ai@dnsc.ro



 Download File
Download File